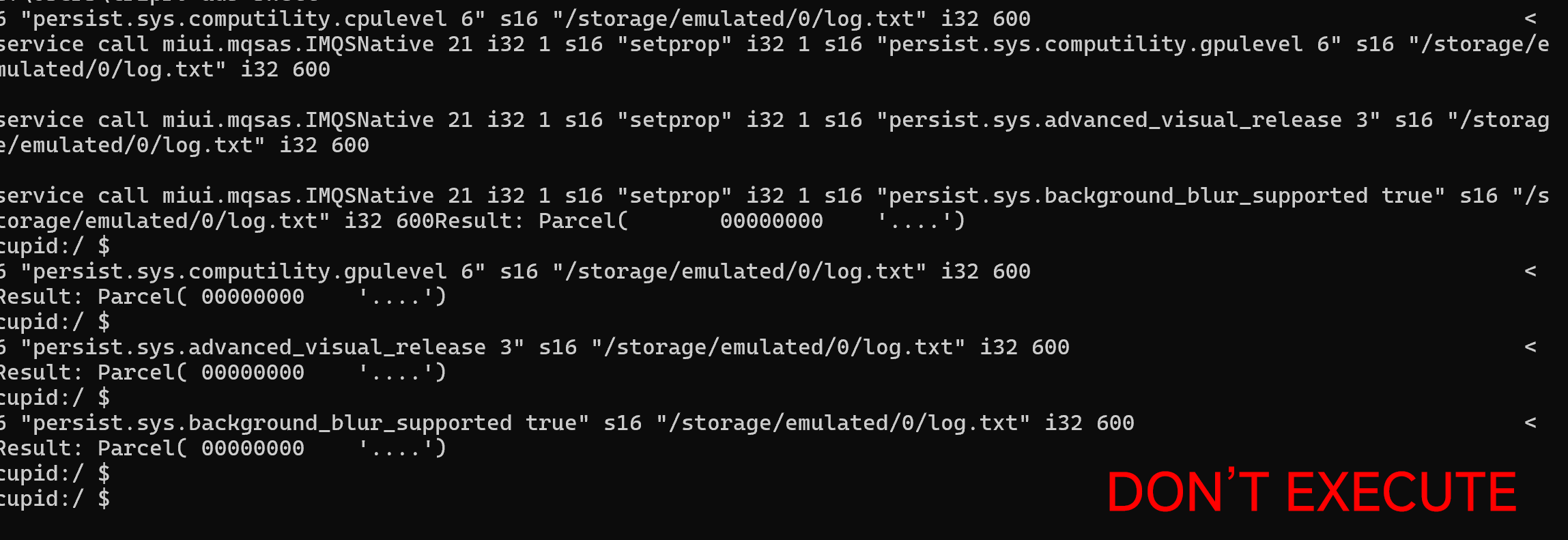
A serious security vulnerability currently threatens Xiaomi devices running HyperOS 1 through HyperOS 3. Malicious actors can use a specific line of code to exploit the system and gain unauthorized root privileges. This dangerous exploit leaves devices completely vulnerable to malware injection and can cause severe system damage.
-
The exploit code: The vulnerability is triggered through specific ADB commands containing [code snippet missing]
miui.mqsas.IMQSNative. Executing this code instantly grants full system permissions as if the device were fully rooted. -
Risks: This vulnerability allows malicious software to be injected directly into your phone. It can completely break your operating system or give attackers total control over your personal data.
How does the Xiaomi root exploit work?
The exploit works by tricking your phone’s built-in diagnostic tools into accepting unauthorized commands. When a user connects their device to a computer, this code bypasses normal security checks and communicates directly with the operating system kernel.
-
The entry point: Attackers use an Android Debug Bridge (ADB) connection to send text-based commands directly from a computer to the phone.
-
The target service: The code specifically targets this service
miui.mqsas.IMQSNative. It is a deep system service within Xiaomi HyperOS that typically handles background quality reports and system diagnostics. -
The root trick: By sending a carefully crafted message
llamada de servicioto this diagnostic tool, the attacker forces the phone to change basic system settings (such as root accesssetprop). Because the diagnostic tool already has high-level permissions, it executes the malicious command with the same power as a fully rooted device, even though the phone’s bootloader is locked.
This deep access to the system is precisely why the vulnerability is so dangerous and why the upcoming security patch in March 2026 is critical for all users.
How can you protect yourself from this vulnerability?
Disabling USB debugging on your Xiaomi phone is the best immediate defense against this serious exploit. This action completely closes the digital bridge that attackers use to send malicious commands from a computer to your device. Disabling this feature ensures that your personal data remains safe until the official patch is released.
-
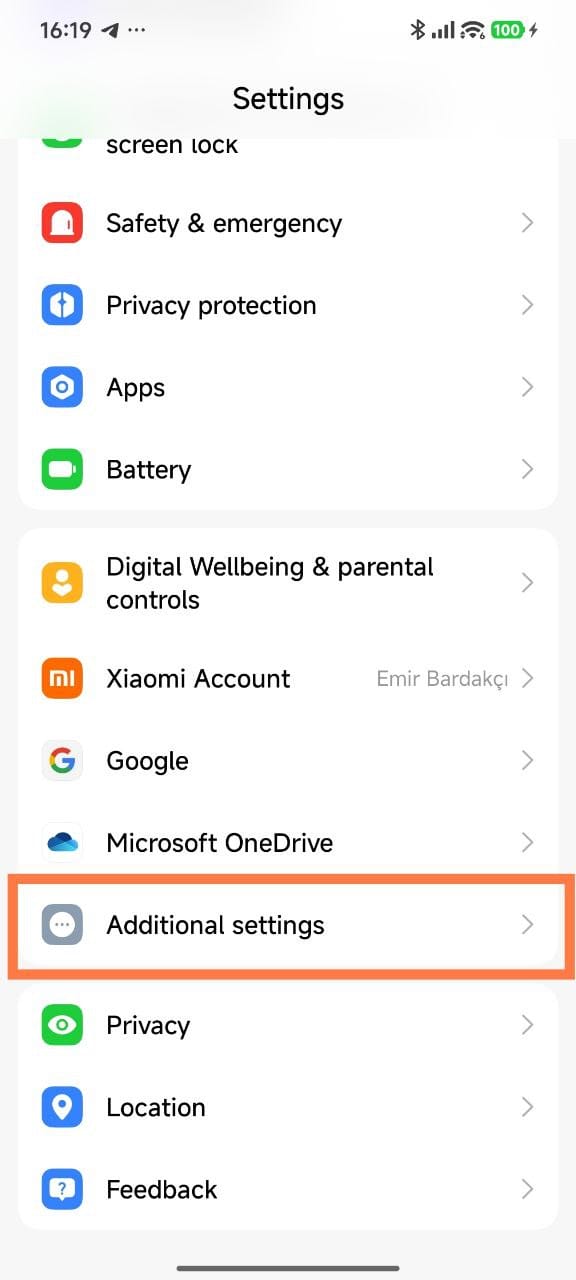
Open Settings: Unlock your phone and open the standard Settings app.
-
Locate Additional Settings: Scroll down the menu and tap on the Additional Settings section.
-
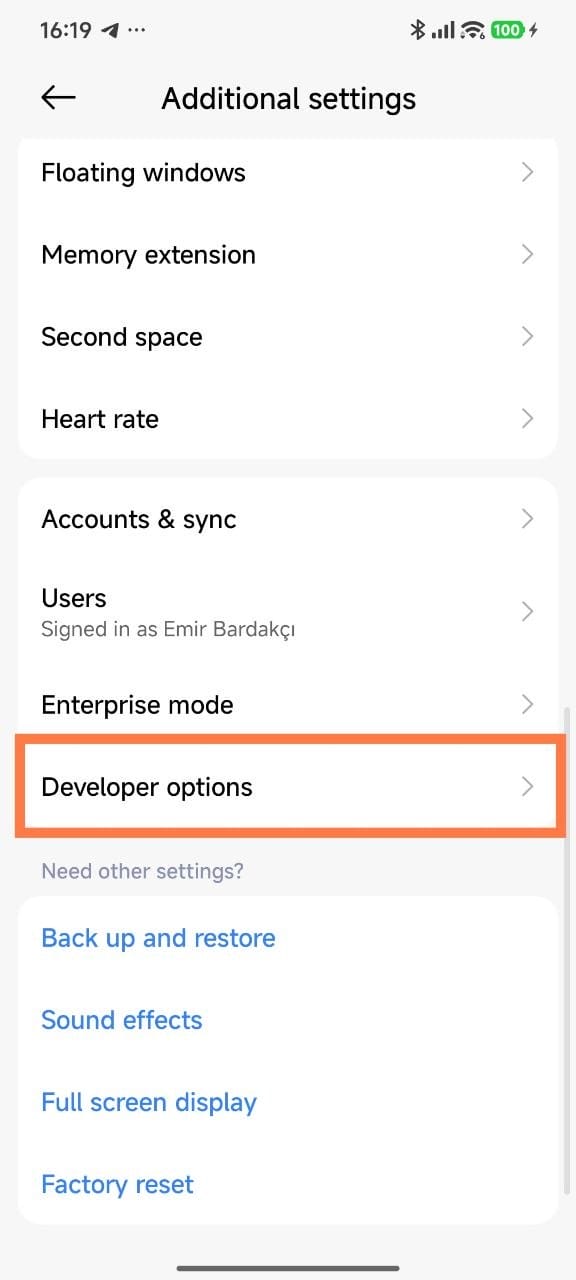
Access Developer Options: Scroll to the bottom of this menu and select Developer Options. If you don’t see this menu, the feature is already hidden and disabled on your device.
-
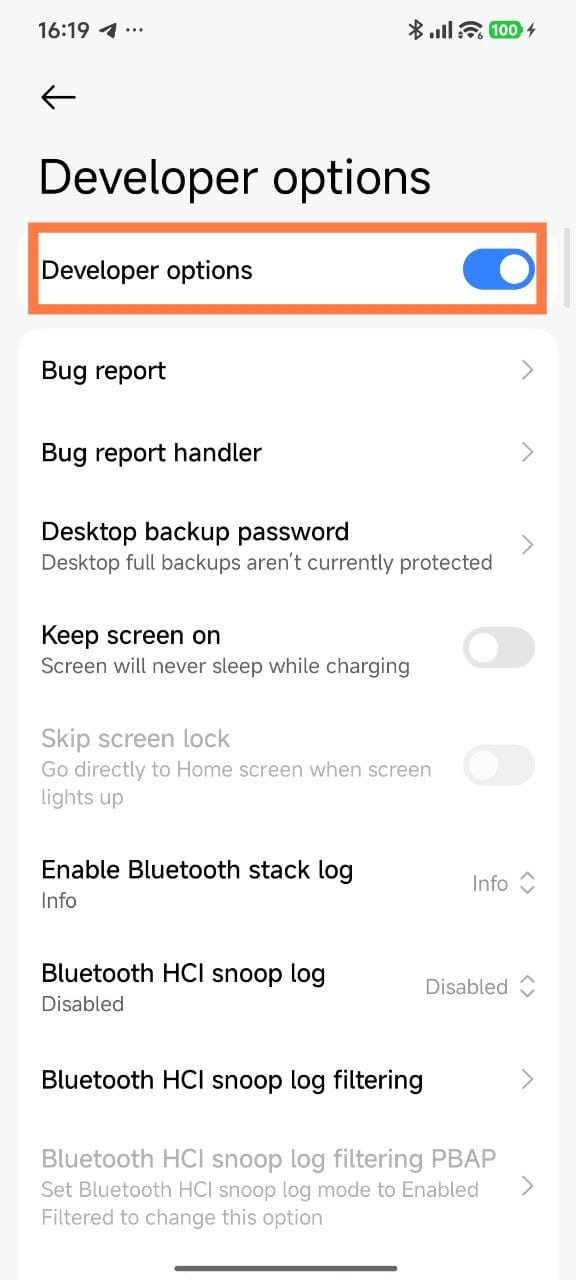
Disable USB Debugging: Locate the toggle switch labeled «USB Debugging» and turn it off.
-
Revoke previous connections: Tap the option that says «Revoke USB debugging authorizations» to erase the memory of devices you connected to in the past.
Which devices does it affect?
This dangerous security vulnerability currently exists on all devices running Xiaomi HyperOS 1 to Xiaomi HyperOS 3.
- Xiaomi 11T
- Redmi 13C 5G, Redmi 13R
- Xiaomi Mi 11X, Xiaomi POCO F3, Xiaomi Redmi K40
- Redmi Note 14 Pro
- POCO F8 Pro, REDMI K90
- POCO C81, REDMI A7 Pro
- Xiaomi Poco F3 GT, Xiaomi Redmi K40 Gaming
- Xiaomi 13T
- Xiaomi 14 Ultra
- Xiaomi Mix Fold 3
- POCO M7 Pro 5G, Redmi Note 14
- Xiaomi MIX FLIP 2
- POCO C61, Redmi A3
- POCO M6 Plus 5G, Redmi 13 5G, Redmi Note 13R
- Xiaomi Mi 10 Ultra
- Xiaomi Mi MIX FOLD
- REDMI Note 15 Pro 4G
- Xiaomi 14 CIVI, Xiaomi Civi 4 Pro
- Xiaomi Mi 10 Pro
- Redmi K60 Ultra, Xiaomi 13T Pro
- POCO M7 4G, REDMI 15 4G
- Xiaomi 12
- Xiaomi 15
- Xiaomi Pad 5 Pro 12.4
- REDMI K80 Ultra
- POCO X8 Pro Max, REDMI Turbo 5 Max
- Xiaomi 12 Pro Dimensity Edition
- Xiaomi 14T
- POCO C85 4G, REDMI 15C 4G
- Xiaomi 15S Pro
- Redmi K50 Ultra, Xiaomi 12T Pro
- POCO Pad, Redmi Pad Pro
- POCO X6 Pro, Redmi K70E
- POCO C55, Redmi 12C
- Xiaomi Pad 5 Pro Wi-Fi
- POCO M6 Pro 4G, Redmi Note 13 Pro 4G
- Redmi Note 14S
- Xiaomi Pad 5 Pro 5G
- Xiaomi Redmi Note 11, Xiaomi Redmi Note 11T 5G
- Xiaomi Poco M4 Pro 5G
- Redmi 12
- POCO M7 5G, Redmi 14R 5G
- Redmi Pad SE 8.7 Wi-Fi
- POCO M4 Pro, Redmi Note 11S
- POCO M8 Pro 5G, REDMI Note 15 Pro+
- POCO Pad M1, Redmi Pad 2 Pro
- Xiaomi 13
- POCO C65, Redmi 13C
- POCO X6 5G, Redmi Note 13 Pro
- Xiaomi MIX FOLD 4
- POCO X6 Neo, Redmi Note 13 5G, Redmi Note 13R Pro
- Xiaomi 15T
- Xiaomi 15 Pro
- Xiaomi Mi 11i, Xiaomi Mi 11X Pro, Xiaomi Redmi K40 Pro, Xiaomi Redmi K40 Pro+
- Xiaomi 14
- POCO F4 GT, Redmi K50 Gaming
- Xiaomi 13 Ultra
- Xiaomi Pad 7 Ultra
- POCO X8 Pro, POCO X8 Pro Edición Iron Man, REDMI Turbo 5
- Redmi A3x
- Xiaomi 15T Pro
- REDMI Pad 2 4G
- POCO M8 5G, REDMI Note 15 5G
- POCO C75, Redmi 14C, Redmi A3 Pro
- REDMI Note 15 Pro
- POCO M4 5G, Redmi 10 5G, Redmi 10 Prime+ 5G, Redmi 11 Prime 5G, Redmi Note 11E
- Redmi Note 11R
- Xiaomi 11 Lite 5G NE, Xiaomi Mi 11 LE
- Xiaomi Pad 6 Pro
- Xiaomi CIVI 5 Pro
- POCO X7, Redmi Note 14 Pro
- Redmi K70 Pro
- POCO F5 5G, Redmi Note 12 Turbo
- POCO F4 Pro, Redmi K50 Pro
- Xiaomi 12S
- POCO F7 Ultra, REDMI K80 Pro
- Xiaomi Civi
- POCO F5 Pro, Redmi K60
- POCO M6, Redmi 13, Redmi 13X
- POCO X5 5G
- POCO F4, Redmi K40S
- Xiaomi Pad 7 Pro
- POCO F8 Ultra, REDMI K90 Pro Max
- Xiaomi Pad 5
- Xiaomi 17 Ultra, Xiaomi 17 Ultra Leica y Leitzphone
- Xiaomi 13 Pro
- Redmi Note 14 Pro 4G
- Xiaomi Mix 4
- POCO F7, REDMI Turbo 4 Pro
- Redmi Note 11S 5G
- REDMI Pad 2 Pro 5G
- Xiaomi 17 Pro
- Redmi Note 12T Pro
- POCO F6, Redmi Turbo 3
- Xiaomi Pad 8 Pro
- Xiaomi Pad 6
- Xiaomi 11i, Xiaomi 11i HyperCharge, Xiaomi Redmi Note 11 Pro, Xiaomi Redmi Note 11 Pro+
- Xiaomi 12T
- Xiaomi 17 Pro Max
- Xiaomi 12X
- Xiaomi 17
- POCO X5 Pro 5G, Redmi Note 12 Pro Speed Edition
- Redmi K60E
- POCO M5, Redmi 11 Prime
- POCO X7 Pro, REDMI Turbo 4
- Redmi K70 Ultra, Xiaomi 14T Pro
- Redmi Pad Pro 5G
- Redmi K50
- Redmi Note 12 Explorer (Discovery), Redmi Note 12 Pro, Redmi Note 12 Pro+
- Xiaomi MIX FLIP
- Redmi Note 13 4G
- Redmi Note 13 4G NFC
- Redmi Note 12S
- Xiaomi Pad 6S Pro 12.4
- Xiaomi 14 Pro
- POCO M6 Pro, Redmi 12 5G, Redmi Note 12R
- Redmi K60 Pro
- POCO C85x, REDMI 15A 5G, REDMI 17 5G, REDMI A7 Pro 5G India
- Redmi Pad SE 4G
- Redmi Note 11
- Redmi Note 11 NFC
- POCO M7 Plus, POCO M8s, REDMI 15
- Xiaomi Mi 11 Pro, Xiaomi Mi 11 Ultra
- Redmi Note 12, Redmi Note 12R Pro
- Xiaomi Redmi Note 10 Pro
- Redmi Note 12 Pro 4G
- REDMI Pad 2
- Redmi Note 14 4G
- Xiaomi 12 Lite
- Redmi Note 12 4G
- Xiaomi 12S Ultra
- Xiaomi Mi 10S
- Redmi Note 12 NFC 4G
- POCO C85 5G, REDMI 15C 5G
- REDMI K Pad, Xiaomi Pad Mini
- POCO Pad X1, Xiaomi Pad 7
- Xiaomi Mi 10
- Xiaomi 12S Pro
- Xiaomi Mi 11
- POCO F6 Pro, Redmi K70
- POCO X4 Pro 5G, Redmi Note 11E Pro, Redmi Note 11 Pro+ 5G, Xiaomi Redmi Note 11 Pro 5G
- Redmi Note 11 Pro 4G India
- Xiaomi 11T Pro
- Xiaomi iPad 7S Pro 12.5
- Redmi Note 11 Pro 4G
- POCO C75 5G, Redmi A4
- POCO X4 GT, POCO X4 GT Pro, Redmi K50i, Redmi K50i Pro, Redmi Note 11T Pro, Redmi Note 11T Pro+
- Xiaomi 15 Ultra
- Redmi Pad SE
- Xiaomi iPad 6 Max 14
- Xiaomi Civil 3
- Xiaomi Redmi Pad
- Xiaomi Pad 8
- Xiaomi 12 Pro
- Xiaomi Civic 1S
- Redmi Note 13 Pro+
- Xiaomi 13 Lite, Xiaomi Civi 2
- Xiaomi MIX FOLD 2
- POCO F7 Pro, REDMI K80
Your phone is now secure against unauthorized wired connections and safe from this specific ADB exploit. Remember to install the March 2026 security patch for Xiaomi HyperOS as soon as it appears in your update menu.
Xiaomi will provide a permanent fix through the March 2026 security patch via system updates. You should avoid running unknown ADB commands on your device and install this upcoming update as soon as it appears in your settings menu.


 Emir Bardakçı
Emir Bardakçı