As of March 21, 2026, a perfect storm of security vulnerabilities is converging on the Xiaomi user base, and the company’s essential response—the HyperOS March 2026 security update—is dangerously absent.
While millions of devices remain unprotected, the security community is sounding the alarm on a triple threat of critical exploits that can lead to total device compromise. The current situation is simple but terrifying: Until this patch arrives, virtually every Xiaomi, Redmi, and POCO smartphone is an easy target.
A Dangerous Trio of Unpatched Vulnerabilities
The delay of the March 2026 patch isn’t just slow; it is a catastrophe, as the missing update is the only known defense against three distinct and severe flaws.
1. The Trusted Execution Environment (TEE) Exploit
Exposed by security researchers at Ledger’s Donjon, this hardware-level vulnerability targets the Secure World of a smartphone’s processor (TEE). This secure enclave is supposed to protect your most sensitive data: biometric templates, screen locks (PIN/Pattern), and cryptographic seed phrases for wallets.
Researchers demonstrated that attackers with physical access can bypass the entire Android operating system and extract this critical data in less than 60 seconds. This flaw affects a vast number of both MediaTek and Snapdragon chipsets, placing a massive portion of Xiaomi’s portfolio at risk of financial and personal identity theft.
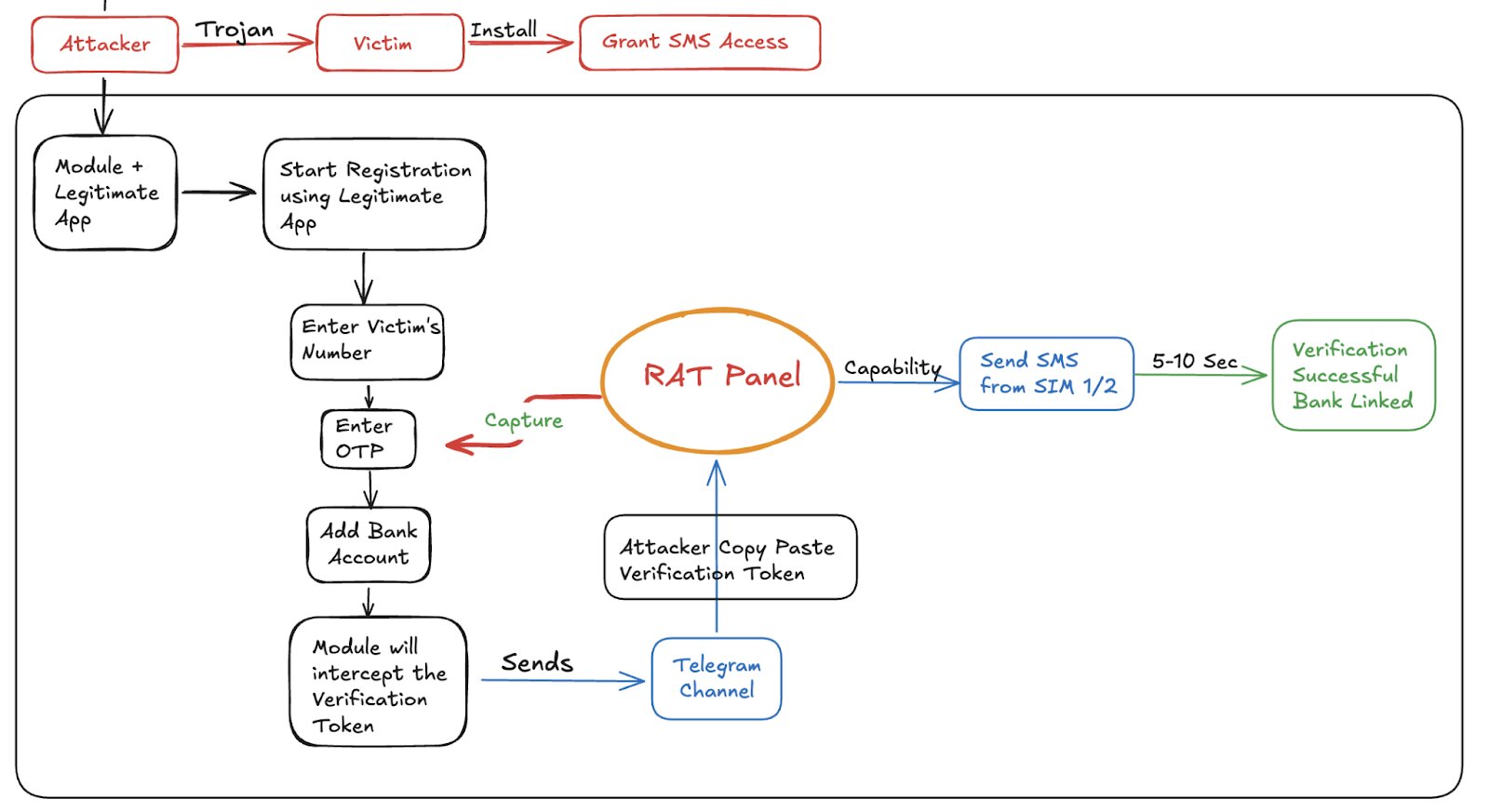
2. The HyperOS ADB Root-Like Exploit (HyperOS 2 & 3)
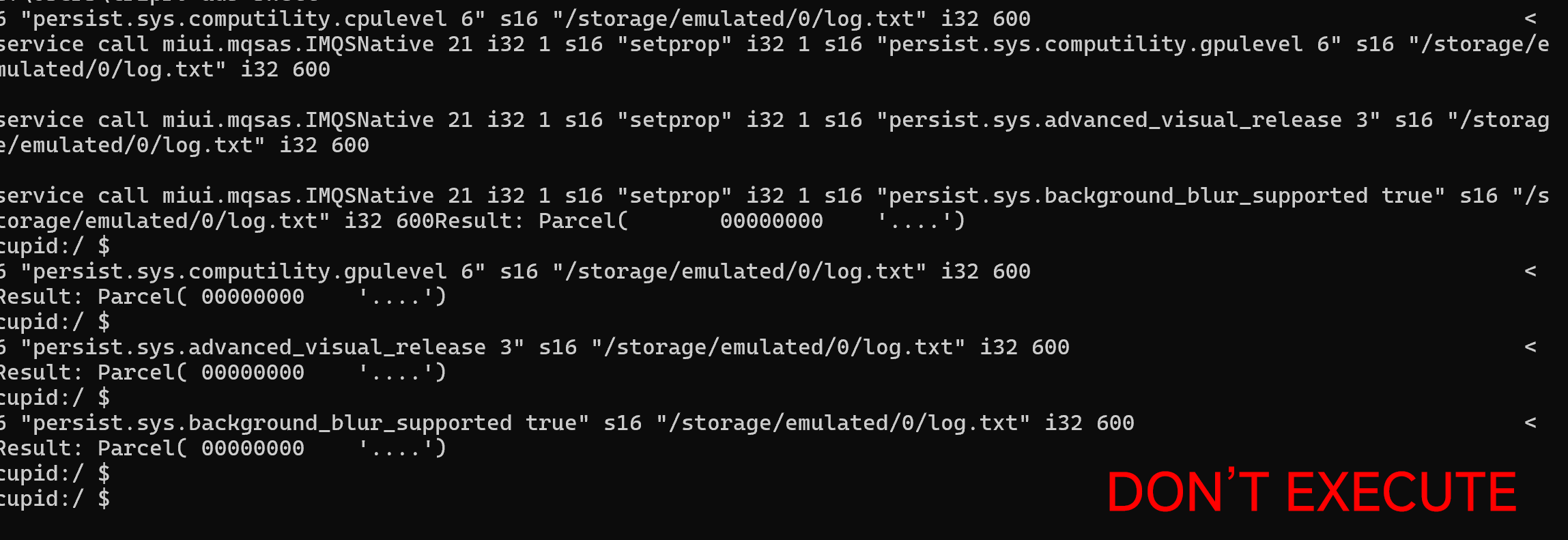
A devastating new software-level exploit has been identified within the core of HyperOS versions 2 and 3 (which includes the current Android 15-based versions). This flaw allows any user with standard Android Debug Bridge (ADB) access—typically used for developing or sideloading—to execute commands with the same level of permission as a rooted device.
This means that a malicious party with physical or ADB access can hijack the device, bypass standard permission dialogs, and even steal non-TEE protected data, all without triggering the typical security warnings associated with a real root. It effectively dismantles the security sandboxing model that Android relies on.
3. The Snapdragon 8 Elite Gen 5 Fastboot Bootloader Unlock
In perhaps the most stunning hardware security failure, an exploit has been discovered in Qualcomm’s latest flagship chipset, the Snapdragon 8 Elite Gen 5. While a bootloader unlock normally involves wiping a device to protect user data, this exploit allows an attacker to unlock the bootloader of a flagship phone simply by flashing a single file via the standard Fastboot protocol.
This method circumvents all security protocols, giving attackers full access to the file system and making it trivial to install persistent spyware or compromise any security layers. It is an immediate and total compromise of a premium device’s integrity.
What You MUST Do Now to Protect Yourself
Until Xiaomi releases the March 2026 patch for your specific model, your device is in the danger zone. Users must take extreme, manual precautions immediately:
-
Guard Your Device Like Your Wallet: All three exploits, particularly the TEE and Fastboot flaws, require physical access or ADB connectivity. Turn off DEVELOPER OPTIONS if it’s on.
-
Disable USB Debugging Immediately: If you use ADB or have USB Debugging enabled (in Developer Options), disable it immediately. A HyperOS ADB exploit makes this setting a massive back door.
-
Be Extremely Vigilant Against Phishing: Avoid installing any apps from outside the official Google Play Store, and do not connect your device to any unfamiliar computers via USB.
-
Monitor for Updates Daily: Do not wait for an OTA notification. Manually check your HyperOS updater or MemeOS Enhancer app multiple times a day. The moment the March 2026 patch appears, install it.
Xiaomi, the clock is not ticking; it is a siren. A critical mass of your user base is exposed to three simultaneous, catastrophic security risks. Expedite the HyperOS March 2026 update rollout immediately before massive financial and identity losses begin.






Now Update Too bad Give Me Hyper OS 3
This feels a bit exaggerated. The vulnerabilities mentioned mostly require physical access or USB debugging to be enabled, which isn’t the case for most users. It’s good to be aware, but calling all devices “under threat” makes it sound worse than it actually is.
man I don’t even have HyperOS 3
It’s unbelievable how long it takes Xiaomi to deliver the necessary patch when almost all phones are at risk. It is common practice that the security patch arrives 1 to 2 months later than it should. Xiaomi is playing with customers’ trust, and if this continues, I will not return to this brand.
It’s unbelievable how long it takes Xiaomi to deliver the necessary patch when almost all phones are at risk. It is common practice that the security patch arrives 1 to 2 months later than it should. Xiaomi is playing with customers’ trust, and if this continues, I will not return to this brand.
It’s unbelievable how long it takes Xiaomi to deliver the necessary patch when almost all phones are at risk. It is common practice that the security patch arrives 1 to 2 months later than it should. Xiaomi is playing with customers’ trust, and if this continues, I will not return to this brand.
It’s unbelievable how long it takes Xiaomi to deliver the necessary patch when almost all phones are at risk. It is common practice that the security patch arrives 1 to 2 months later than it should. Xiaomi is playing with customers’ trust, and if this continues, I will not return to this brand.
It’s unbelievable how long it takes Xiaomi to deliver the necessary patch when almost all phones are at risk. It is common practice that the security patch arrives 1 to 2 months later than it should. Xiaomi is playing with customers’ trust, and if this continues, I will not return to this brand.
2 months that the Poco X7 Pro has not received any update while the performance is really very bad. Xiaomi doesn’t care about people and doesn’t care about customers and focuses only on attracting new customers. After 10 years with Xiaomi, I will go to the competition next time I have to buy a phone or something else.
Typical of Xiaomi