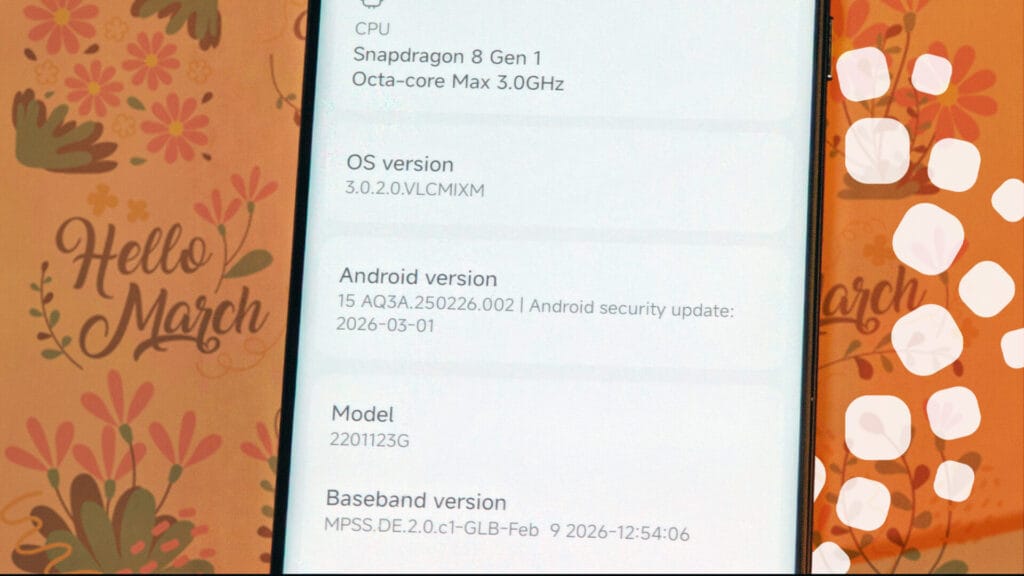
Google has officially released the March 2026 Android Security Bulletin, detailing a comprehensive set of patches for the Android. While Xiaomi has not yet initiated the OTA rollout for its HyperOS devices, the technical documentation provides a clear roadmap of the security enhancements and system optimizations currently in the integration phase.
This report summarizes the critical vulnerabilities and component-specific fixes that will be implemented in the upcoming Xiaomi firmware updates.
Overview of Vulnerability Metrics
The March 2026 update addresses a total of 129 vulnerabilities across various system layers. Every vulnberabilities is not important. These are categorized by their impact on the Android Open Source Project (AOSP) and third-party vendor components (Qualcomm, MediaTek, etc.).
| Component | Most Severe Impact | Critical CVEs |
| Framework | Local Escalation of Privilege (EoP) | CVE-2026-0047 |
| System | Remote Code Execution (RCE) | CVE-2026-0006 |
| Kernel | Local Escalation of Privilege (EoP) | CVE-2024-43859, CVE-2026-0037 |
| Qualcomm | Buffer Over-read / Graphics | CVE-2026-21385 |
Core System Vulnerabilities (AOSP)
The 2026-03-01 patch level focuses on the Framework and System partitions.
-
Remote Code Execution (CVE-2026-0006): Identified in the System component, this vulnerability allows for remote code execution without requiring additional execution privileges or user interaction. This is the highest priority fix for the March cycle.
-
Privilege Escalation (CVE-2026-0047): A critical vulnerability in the Framework that allows a local attacker to gain elevated system privileges.
-
Denial of Service (CVE-2025-48631): A critical vulnerability within the System layer that can lead to remote denial of service (DoS), potentially causing system instability or boot loops.
Kernel and Virtualization Security
The 2026-03-05 patch level introduces critical fixes for the Linux kernel and virtualization modules, which are essential for the security of modern Xiaomi flagships.
-
Flash-Friendly File System (CVE-2024-43859): A critical EoP vulnerability in the F2FS component has been resolved. This fix is vital for devices utilizing high-speed UFS storage, ensuring file system integrity.
-
pKVM and Hypervisor: Multiple critical vulnerabilities (CVE-2026-0037, CVE-2026-0038) were patched in the Protected Kernel-Based Virtual Machine (pKVM). These fixes prevent unauthorized access to isolated execution environments.
-
Transport Layer Security (TLS): Several high-severity vulnerabilities in the kernel’s TLS implementation (CVE-2025-38616, CVE-2025-39946) have been addressed to secure data in transit at the OS level.
Vendor-Specific Components (Qualcomm, MediaTek, Unisoc)
Xiaomi’s diverse hardware portfolio requires specific binary updates from silicon providers:
-
Qualcomm: Focuses on display and graphics drivers. CVE-2026-21385 is a notable high-severity vulnerability affecting the display component that requires immediate patching upon the update’s availability.
-
MediaTek: Addresses 20 vulnerabilities, primarily in the Modem and Display subcomponents. These patches resolve issues related to signal stability and display driver vulnerabilities.
-
Unisoc: Fixes 7 high-severity vulnerabilities in the Modem component, relevant for entry-level Redmi devices.
Implementation Status and Recommendations
As of this report, Xiaomi is in the internal testing and integration phase. The March 2026 security patch level has not yet been deployed to the public stable branches.
The rollout is expected to begin mid-March, starting with the Xiaomi 16 and 15 series in the China region, followed by Global and EEA branches. Users are advised to monitor the “System Update” section within HyperOS for the 2026-03-01 or 2026-03-05 security string.

 Emir Bardakçı
Emir Bardakçı


